Product Introduction
A modern log analytics platform that seamlessly offers scalable Search, Security, and Observability solutions powered by open-source tools on commercial cloud data platforms
Customer Success Stories
Discover how Elysium has helped our customers power their mission critical applications while enhancing operational efficiency, and gain valuable insights.

Needed a search and UEBA solution with the essential tools and capabilities required for in-depth analytics of escalated cases in the SOC
Needed a more robust security solution to modernize and elevate the protection of their enterprise and customer data without a considerable cost increase in computing and storage

Needed full observability of incoming data streams: visibility into their ingestion and collection of Boomi and Azure events into the Elysium application
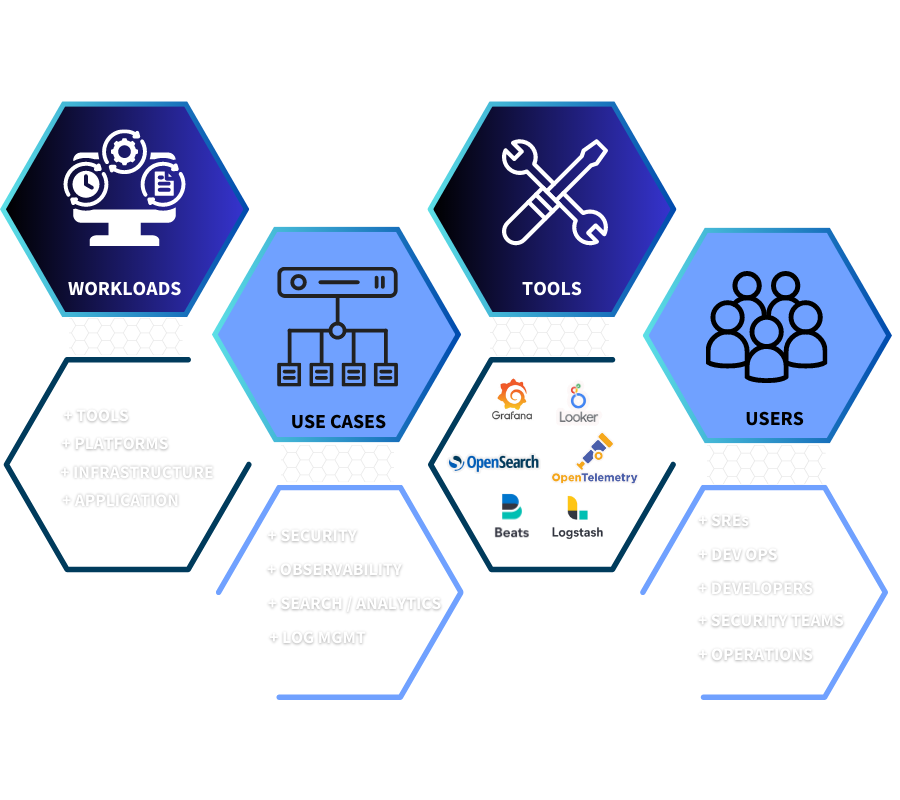
Designed to help every team to do more.
Give teams the precise ways to achieve their goals with a simple user experience and execute the tasks faster
Monitor any stack with 300+ Integrations



